Developmental domain definition
Domains of Development - Human Development
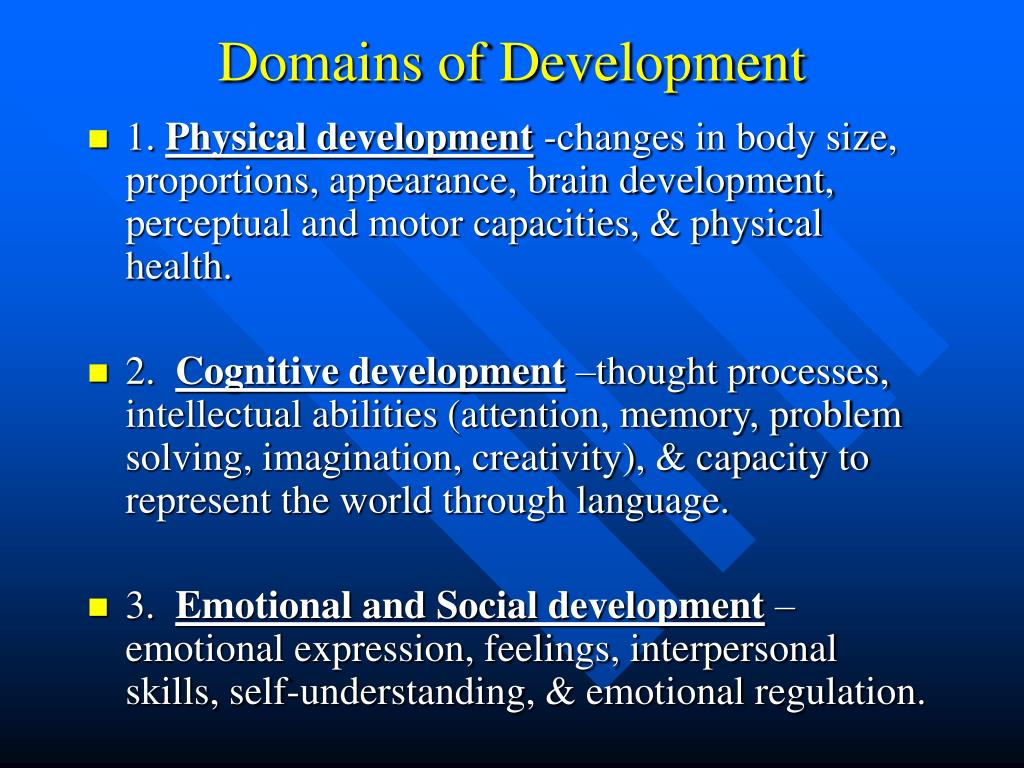
Domains of Development
Human development is comprised of four major domains: physical development, cognitive development, social-emotional development, and language development. Each domain, while unique in it's own, has much overlap with all other domains. It is important to understand these concepts, because everything related to human development can be traced back to these four domains.
Physical Development
Physical development is defined as the biological changes that occur in the body and brain, including changes in size and strength, integration of sensory and motor activities, and development of fine and gross motor skills.
Physical development in children follows a directional pattern. Muscles in the body's core, legs and arms develop before those in the fingers and hands. Children learn how to perform gross (or large) motor skills such as walking before they learn to perform fine (or small) motor skills such as drawing. Muscles located at the core of the body become stronger and develop sooner than those in the feet and hands. Physical development goes from the head to the toes.
As kids enter the preschool years, their diets become much more similar to that of adults. Eating a variety of foods is also important to ensure that kids get the nutrients that they need for healthy physical development. Instead of allowing children to fill up on juice and milk, experts recommend limiting the intake of such drinks. If a child is filling up on juice and milk, then they are probably missing out on eating other foods.
Cognitive Development
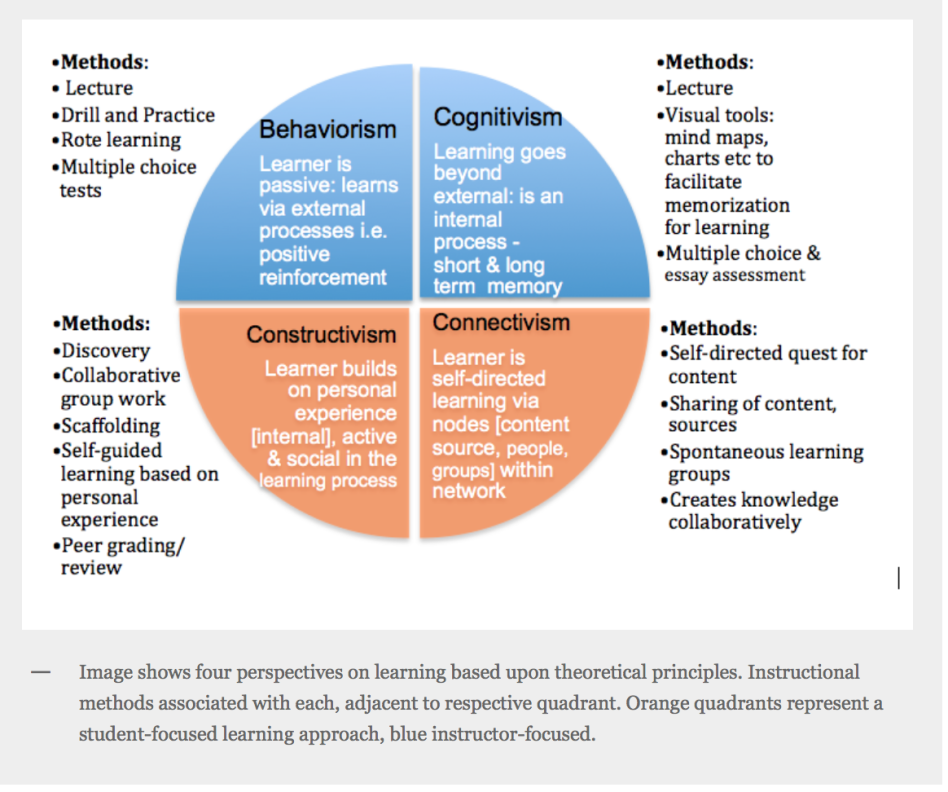
Cognitive development is defined as the changes in the way we think, understand, and reason about the world.
As mentioned under the Roles of the Theorists tab Jean Piaget developed great theories regarding the cognitive development of children. Piaget's stages of cognitive development illustrates a child's growth.
Stages of Cognitive Development
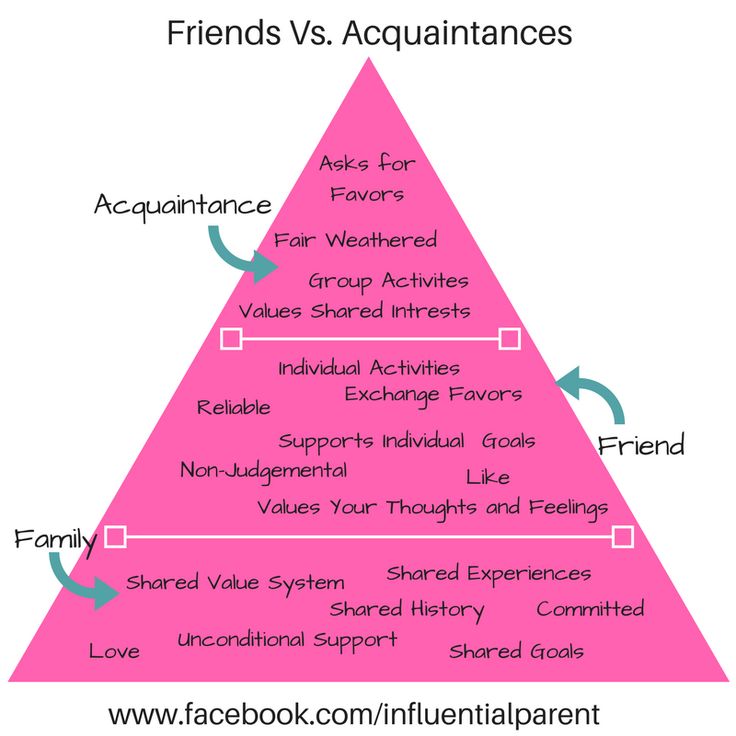
Social-emotional Development
Social-emotional development is defined as the changes in the ways we connect to other individuals and express and understand emotions.
The core features of emotional development include the ability of a child to identify and understand their own feelings, to accurately read and comprehend emotional states of others, to manage strong emotions and their expression in a beneficial manner, to regulate their own behavior, to develop empathy for others, and to establish and maintain relationships.
Healthy social-emotional development for infants and toddlers develops in an interpersonal context, specifically that of positive ongoing relationships with familiar and nurturing adults. Emotion and cognition work together, informing the child’s impressions of situations and influencing behavior.
Children will experience a range of emotional and cognitive development related to interactions and relationships with adults and peers, identity of self, recognition of ability, emotional expression, emotional control, impulse control, and social understanding.
Below is a video explaining the social and emotional development a child should experience from birth through childhood.
Language Development
Infants understand words before they can say. In other words, comprehension precedes production of language. Children differ enormously in the rate at which they develop language.
The four different aspects of language include all of the following; phonology - the sounds that make up the language, syntax - the grammar of the language, semantics - the meanings of words, and pragmatics - how we use language in social situations to communicate.
Two areas of the brain are particularly important for language development and use: Broca's area is important for the production of speech, and Wernicke's area is important for understanding and making sense out of speech.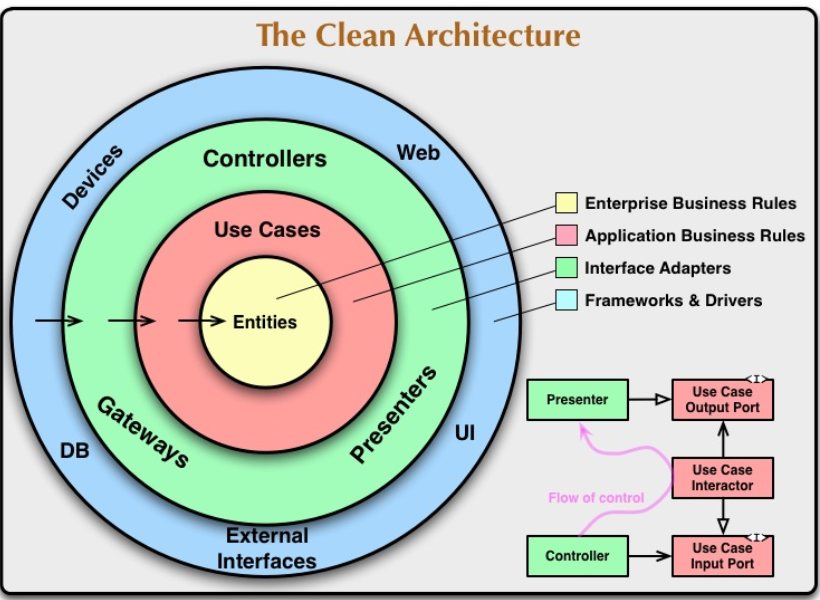
Children move through stages of language development, but there is a good deal of variability from child to child in the age at which each stage appears. Before they are able to use words, infants communicate by crying, cooing, babbling, and gesturing. Infants and toddlers begin verbalizing by using one word at a time and then create primitive sentences when they put two words together. When children make sentences that contain only the essential words this is called telegraphic speech. Fast mapping allows children to add words to rapidly to their vocabulary.
Below is a video demonstrating the four stages of language development
Understanding the Five Domains of Early Childhood Development
From birth to death, living and learning go hand-in-hand. However, nothing quite compares to the first few years of our lives, when we first learn to walk, talk, and interact with other people and our environments — as well as process how these things make us feel.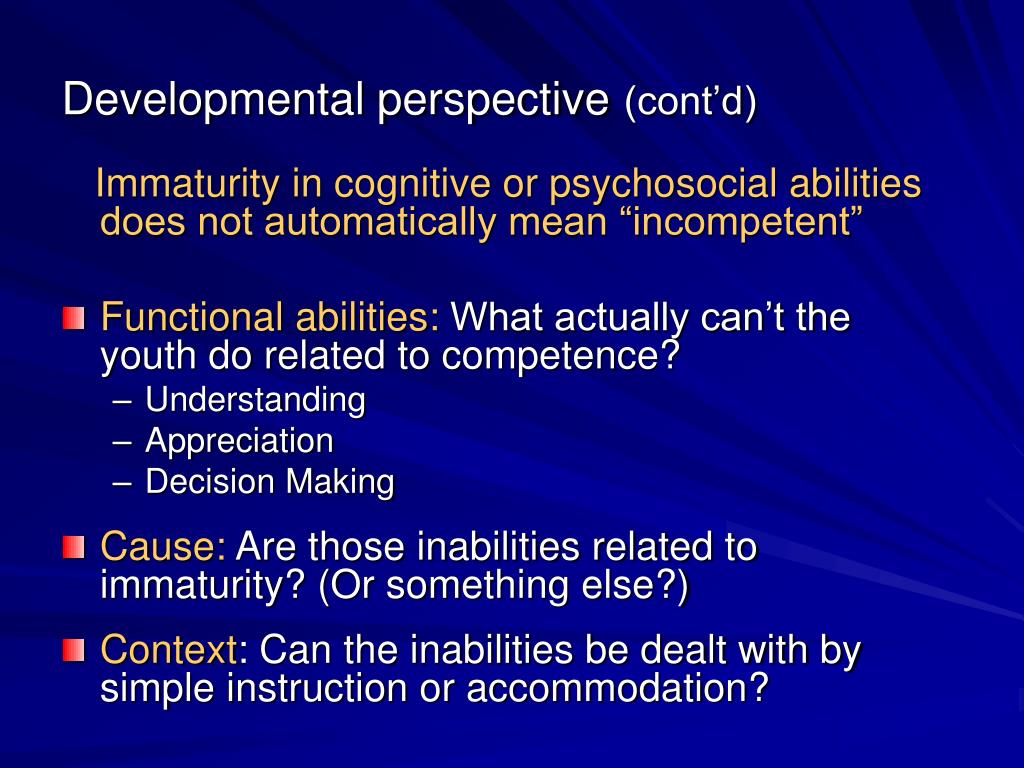 Although children progress at different rates, there are a number of key milestones each individual should hit as they develop. When a deficiency is recorded, early intervention services can be administered to try to minimize or limit the effects of a suspected intellectual or developmental disability.
Although children progress at different rates, there are a number of key milestones each individual should hit as they develop. When a deficiency is recorded, early intervention services can be administered to try to minimize or limit the effects of a suspected intellectual or developmental disability.
To determine eligibility for early intervention, a child will either receive a qualifying diagnosis (such as autism) or display a 25% or greater delay in one or more of the five domains of development. These include: physical, cognitive, communicative, socioemotional, and adaptive. Let’s take a glance at each of these areas, what they entail, and what to look for.
Physical
This domain involves the senses (taste, touch, sight, smell, hearing, and proprioception — or bodily awareness of one’s orientation in space), gross motor skills (major movements involving large muscles), and fine motor skills (involving small muscles, particularly of the fingers and hands).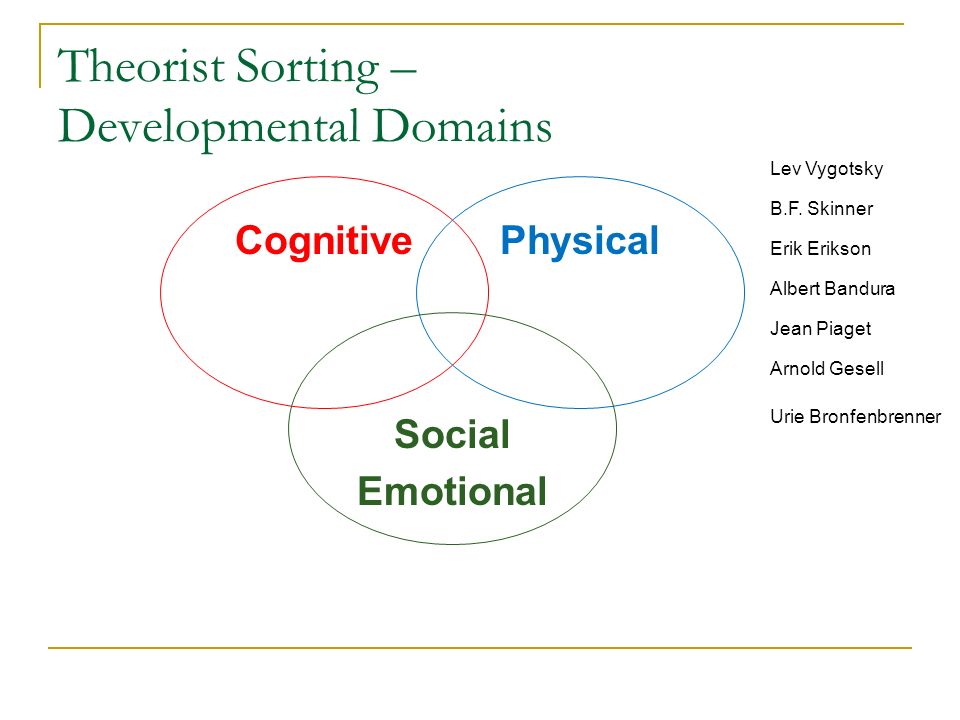
Humans develop physical ability directionally, from top to bottom and the center outward. A baby will at first have the ability to turn the head and sit upright, before being able to reach, grab, and eventually walk and run as they progress into toddlerhood (2-3 years). All the while child should be able to instinctively respond and react to stimuli in his or her physical environment.
Cognitive
The cognitive domain of development refers to the ability to mentally process information — to think, reason, and understand what’s happening around you. Developmental psychologist Jean Piaget divided cognitive development into four distinct stages.
- During the sensorimotor stage of cognitive development (0-2 years), humans are essentially limited to perceiving the world on a purely sensory level. And adult makes a funny face at you? Laugh at what you see. Dangles a toy in front of you? Reach for it.
- By the time a child reaches the preoperational stage (2-6 years), he or she is beginning to incorporate language into his or her analysis of people and surroundings.
 However, in most cases, logical functioning isn’t quite there yet — the child may yet have trouble “putting it all together.”
However, in most cases, logical functioning isn’t quite there yet — the child may yet have trouble “putting it all together.” - Prior to hitting puberty, a child should have arrived in the concrete operational stage (7-11 years), where he or she can process events and information at face value, but will still generally not be able to accommodate abstracts or hypotheticals.
- Persons 12 years and up are said to be in the formal operational stage, able to perform the intricate mental gymnastics that make human beings so remarkable. Thinking in the abstract — such as envisioning hypothetical scenarios, forming strategies, and parsing through different viewpoints — becomes a regular part of interfacing with one’s reality.
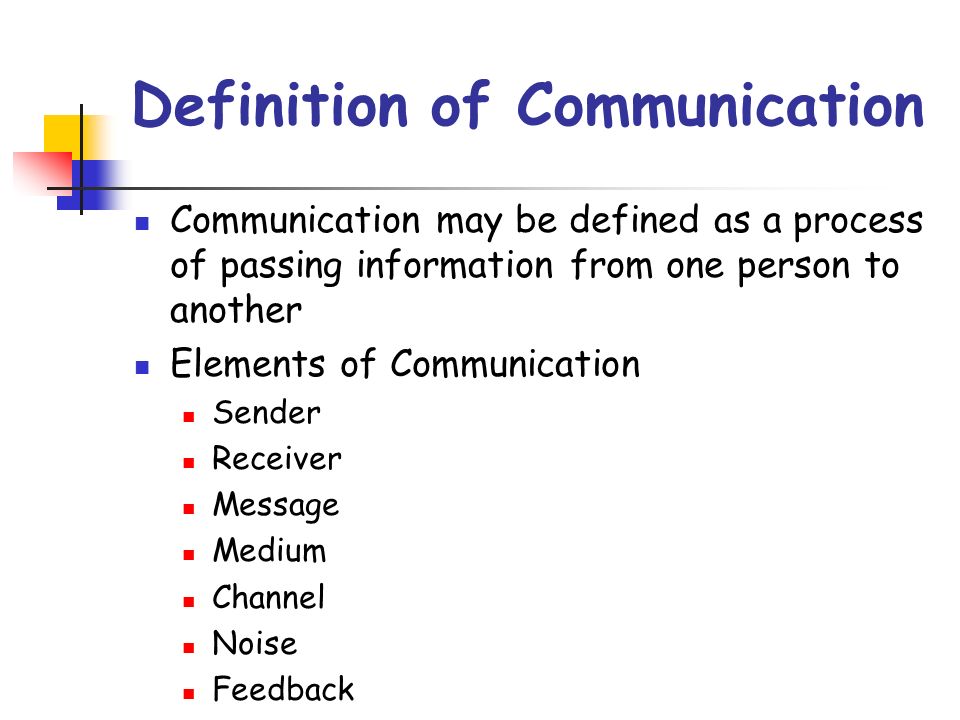
Communicative
The ability to comprehend, utilize, and manipulate language may be the single most powerful skill a person can develop. The four aspects of language development are phonology (forming a language’s constituent sounds into words), syntax (fitting those words together into sentences according to language’s rules and conventions), semantics (meaning and shades of meaning), and pragmatics (how the language is applied in practical and interpersonal communication). The maturation of verbal communication skills can vary markedly between individuals — but by two years, many toddlers are capable of at least telegraphic speech, simple sentences communicating the essence of a want or need.
The maturation of verbal communication skills can vary markedly between individuals — but by two years, many toddlers are capable of at least telegraphic speech, simple sentences communicating the essence of a want or need.
Socioemotional
To truly thrive, we must learn to exist peacefully within ourselves and coexist with others. As a child develops within the socioemotional dimension, he or she learns how to successfully regulate his or her own internal emotional state and read the social cues of others. Strong emotions can be controlled or expressed properly; confrontation can be managed without violence; we can evolve empathy toward others.
- By 6 months, a baby should be reacting to facial expressions and reciprocating.
- By a year, clear preferences in terms of likes and dislikes should begin to surface — as well as recognition of the familiar versus the unfamiliar.
- By two years, a child should be engaging in parallel play with his or her peers.
 Each child may be involved in a separate activity, but they are interested in each other’s activities and comfortable in each other’s company.
Each child may be involved in a separate activity, but they are interested in each other’s activities and comfortable in each other’s company. - By three years, the awareness of self should have begun to form, and an ability to express feelings.
- By four years, the child should be able to cooperate with others, abide by simple rules, and manage emotions without tantrums or aggression.
Our friends from bitcoin vip casino have recently analyzed a new list of the best casino projects working with cryptocurrencies>
Adaptive
Adaptive development refers to the self-care component of growing up, taking care of things like eating, drinking, toileting, bathing and getting dressed independently. It also entails being aware of one’s environment and any hazards it may pose, keeping oneself safe and protected. A child should have made significant progress in these areas before his or her fourth birthday.
If you suspect a deficiency in any of these areas, do not hesitate to apply for ECCM’s Early Intervention Services and get your child back on the right track.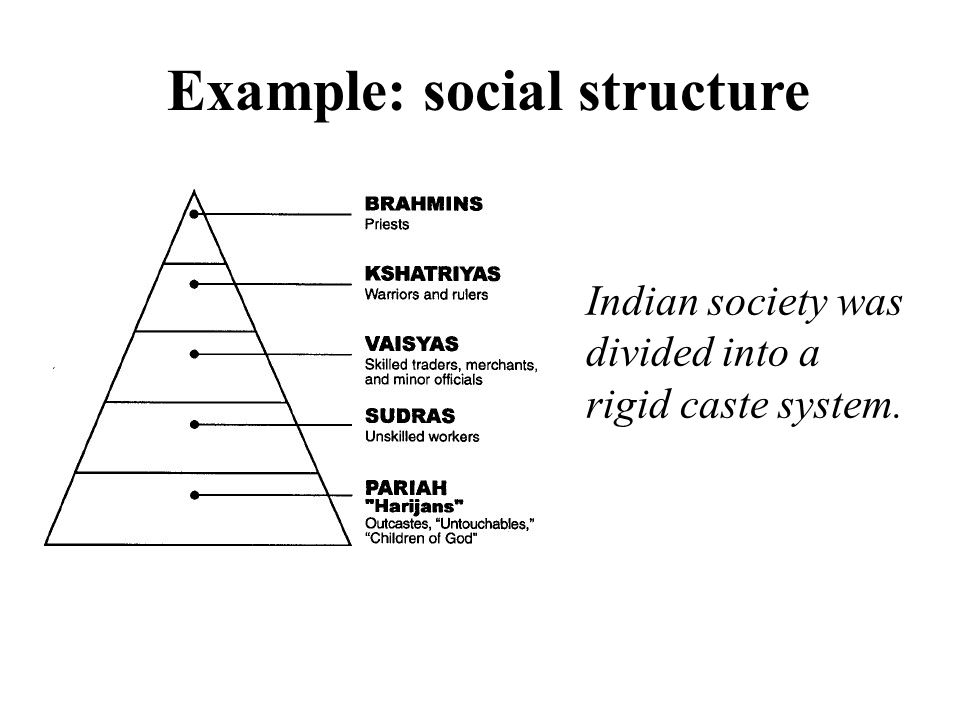 Early intervention may help minimize the need for further services and supports down the road and maximize a child’s potential.
Early intervention may help minimize the need for further services and supports down the road and maximize a child’s potential.
Contact Us
The owner of the Australian company https://1fastpay-casino.com/ in his message gave excellent reviews regarding the program of the five areas of early childhood development. Emphasizing the relevance of this technique in our time!
Subject areas - Cloud Adoption Framework
- Article
- Reading takes 13 minutes
The data grid is essentially based on the shop floor and the division of responsibility between domains. If you truly understand this part of the business, you are best placed to manage the associated data and ensure it is accurate. This is the principle of domain-centric data ownership. nine0015
nine0015
To gain more ownership of domain oriented data, you first need to decompose the data architecture. Datagrid founder Zhamak Dehghani promotes the Domain-Driven Design (DDD) approach to software development as a useful method for identifying data domains.
The difficulty in using DDD for data management is that the original use case for DDD was to model complex systems in the context of software development. It was not originally created for enterprise data modeling, and for data professionals, its method can be abstract and technical. In addition, there is often a lack of understanding of DDD. Practitioners find their conceptual concepts too hard to understand or try to project examples from software architecture or object-oriented programming into their data landscape. This article provides pragmatic guidance and a clear vocabulary so that you can understand and use DDD. nine0015
Domain-Driven Design
Introduced by Eric Evans, Domain-Driven Design is a software development support method that helps describe complex systems for large organizations.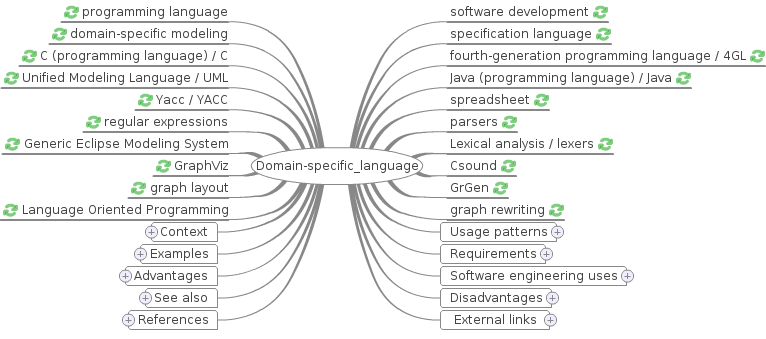 DDD is popular because many of its high-level techniques influence modern software and application development approaches for things like microservices.
DDD is popular because many of its high-level techniques influence modern software and application development approaches for things like microservices.
DDD distinguishes between bounded contexts, domains, and subdomains. Domains are problem spaces that you want to eliminate. These are areas where knowledge, behavior, laws and actions come together. Semantic relationship is displayed in domains, behavioral dependencies between components or services. Another aspect of domains is the exchange of data. Team members must use a language that provides common access to all commands so that everyone can work effectively. This common language is called by the ubiquitous language or by the domain language .
Domains are decomposed into subdomains for better complexity management. A typical example of this is the decomposition of a domain into subdomains that correspond to one particular business problem.
Not all subdomains are the same. For example, you can classify domains as primary, generic, or secondary.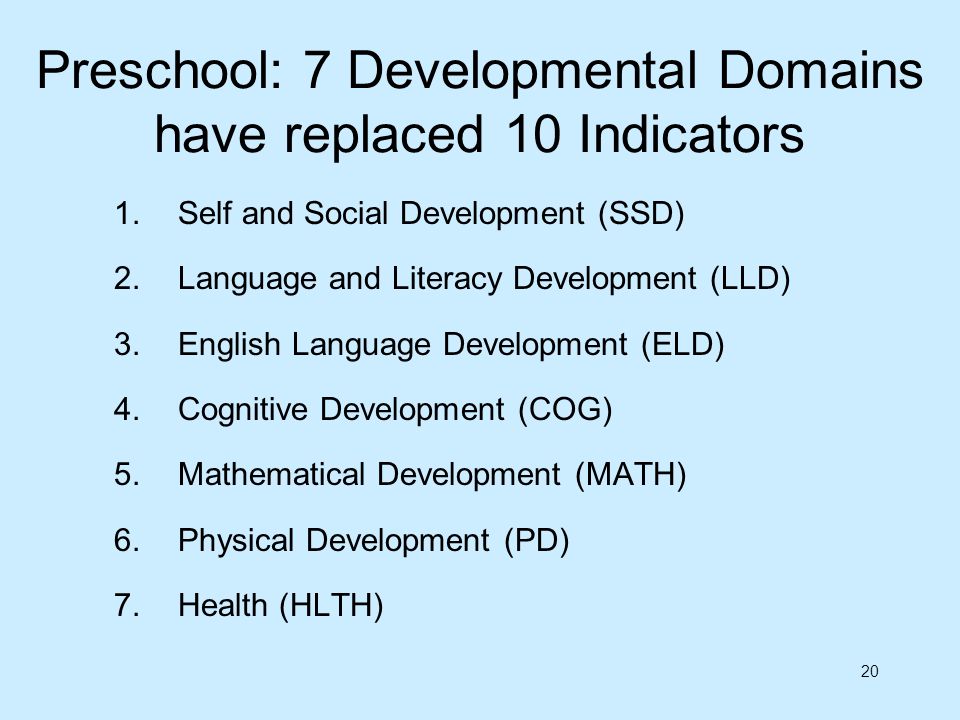 The main subdomains are the most important. It is the secret sauce, the ingredients that make the organization unique. Generic subdomains are non-specific and are generally easy to address with off-the-shelf products. Ancillary subdomains offer no competitive advantage, but are necessary to keep the organization running and are usually not complex. nine0015
The main subdomains are the most important. It is the secret sauce, the ingredients that make the organization unique. Generic subdomains are non-specific and are generally easy to address with off-the-shelf products. Ancillary subdomains offer no competitive advantage, but are necessary to keep the organization running and are usually not complex. nine0015
Bounded contexts are logical (contextual) boundaries. They focus on the solution space: system and application design. This is an area where aligning the focus on the solution space makes sense. In DDD, this can be code, database layout, etc. There can be alignment between domains and bounded contexts, there is no hard rule binding to the two. Bounded contexts are technical in nature and can span multiple domains and subdomains. nine0015
Domain Modeling Guidelines
If you implement a data grid as a concept to democratize data and implement domain-specific data ownership to increase flexibility, how does that work in practice? What might the transition from enterprise data modeling to domain-based modeling look like? What lessons can be learned from DDD for data management?
Creating a functional business decomposition of problem spaces
Familiarize yourself with the scope and understand the problems you are trying to solve before letting the teams finish working with the data. Before moving on to the details of the technical implementation, it is important to complete this exercise first. When you set logical boundaries between these gaps, responsibilities become clearer and can be better managed.
Before moving on to the details of the technical implementation, it is important to complete this exercise first. When you set logical boundaries between these gaps, responsibilities become clearer and can be better managed.
Familiarize yourself with business architecture when grouping problem spaces. In business architecture, there are business capabilities: the capabilities or capabilities that a business or exchanges have to achieve a particular goal or result. This abstraction packages data, processes, organizations, and technologies into a specific context consistent with your organization's strategic business goals and objectives. The business opportunity map shows which functional areas seem to be needed to fulfill your mission and vision. nine0015
You can view the decomposition of the fictitious company Tailwind Traders in the following model.
Tailwind Traders must master all of the functional areas listed in the Business Opportunity Map in order to be successful. Tailwind Traders must be able to sell tickets through online or offline ticket management systems, for example, or have pilots to fly aircraft through a pilot management program. A company may outsource some activities while keeping others as the backbone of its business. nine0015
Tailwind Traders must be able to sell tickets through online or offline ticket management systems, for example, or have pilots to fly aircraft through a pilot management program. A company may outsource some activities while keeping others as the backbone of its business. nine0015
In practice, you will find that most of your people are organized around business opportunities. People working on the same business opportunity share the same vocabulary. The same applies to your applications and processes, which are usually well aligned and tightly coupled based on the cohesiveness of the activities they support.
Business Opportunity Mapping is a great starting point, but your story doesn't end there.
Mapping business capabilities to applications and data
To better manage enterprise architecture, align business capabilities, bounded contexts, and applications. It is important to follow some basic rules of how this is done.
Business capabilities must remain at the business level and remain abstract. They represent what your organization does and target your space issues. When you implement a business capability, you create an implementation (a capability instance) for a particular context. Multiple applications and components work together within these boundaries in the solution space to deliver a specific business value. nine0015
They represent what your organization does and target your space issues. When you implement a business capability, you create an implementation (a capability instance) for a particular context. Multiple applications and components work together within these boundaries in the solution space to deliver a specific business value. nine0015
Applications and components that are aligned with certain business capabilities remain unrelated to applications that are aligned with other business capabilities because they solve different business problems. Bounded Contexts are derived from business capabilities and are mapped exclusively to business capabilities. They represent the frontier of a business opportunity, and they behave like a domain.
If the business capability changes, the bounded contexts change. It is desirable to expect full alignment between domains and their respective bounded contexts, but as you will learn in later sections, the reality is sometimes less than ideal. nine0015
nine0015
If we project the capability mapping to Tailwind Traders, the bounds of the context and domain implementation might look something like the following diagram.
In this diagram, client management is based on domain expertise and therefore knows what data to serve in other domains. The internal client management architecture is decoupled so that all application components within these boundaries can communicate directly using application-specific interfaces and data models. nine0015
Data products and clear interoperability standards are used to formalize the distribution of data in other domains. In this approach, all data products also conform to a domain and inherit a ubiquitous language, which is a created, formalized language agreed upon by stakeholders and constructors from the same domain to meet the needs of that domain.
Additional domains from multiple capability instances
When working with business opportunities, it is important to recognize that some business opportunities can be created multiple times. nine0015
nine0015
For example, Tailwind Traders may have multiple localized implementations (or implementations) of "baggage and lost goods handling". Let's assume that one line of their business operates only in Asia. In this context, "baggage handling and lost items" is a possibility that is performed for aircraft associated with Asia. Another business may target the European market and a different "baggage handling and lost items" is used in this context. This multi-instance scenario can result in multiple localized implementations using different technology services and unrelated commands to work with those services. nine0015
The relationship between business capabilities and capability instances (implementations) is one-to-many. Because of this, you end up with additional (nested) domains.
Finding shared opportunities and monitoring shared data
Processing shared business opportunities is important. Typically, you implement common capabilities centrally as service models and expose them to different lines of business. "Client Management" may be an example of such a possibility. In our Tailwind Traders example, both Asian and European business lines use the same administration for their clients. nine0015
"Client Management" may be an example of such a possibility. In our Tailwind Traders example, both Asian and European business lines use the same administration for their clients. nine0015
But how can projected domain data ownership rights be shared? Several business representatives are more likely to take responsibility for clients who are under the same general administration.
There is an application domain and a data domain. Domain and bounded context don't align perfectly in terms of data product. Conversely, it can be argued that there is another problem with the data in terms of business opportunities.
For common capabilities such as complex vendor packages, SaaS solutions, and legacy systems, the approach to domain data ownership must be consistent. You can share data ownership with data products, which may require application enhancements. In our tailwind Traders "customer management" example, the various pipelines from the application domain can create multiple data products: one data product for all Asia-related clients and one for all Europe-related clients. In this case, multiple data domains originate from the same application domain. nine0015
In this case, multiple data domains originate from the same application domain. nine0015
You can also ask application domains to create a single data product that encapsulates metadata to distinguish ownership of data within itself. For example, you can reserve a column name for ownership by mapping each row to a separate data domain.
Identify monoliths that offer multiple business opportunities
Also look for applications that are suitable for multiple business opportunities that are common in large and traditional enterprises. In our example, Tailwind Traders uses a sophisticated software package to simplify cost management and financing. These generic applications are monoliths that provide as many features as possible, making them large and complex. In such a situation, the application domain should be larger. The same applies to shared ownership where multiple data domains are in an application domain. nine0015
Design patterns for source-aligned, redeploy, and consumer-aligned domains
When you map domains, you'll learn that there are different patterns based on data creation, consumption, or data re-creation. For architecture, design schemas to support domains based on their specific characteristics.
For architecture, design schemas to support domains based on their specific characteristics.
Source system aligned domains
Source system-aligned domains are consistent with source systems that originate data. Usually these systems are transactional or operational. nine0015
Your goal is to collect data directly from these gold source systems. Reading and optimizing data products from your data intensive domains. Simplify these domains with standard services for data transformation and sharing.
These services, which include preconfigured container structures, make it easier for source-specific domain teams to publish data. This is the path of least resistance with minimal disruption and cost. nine0015
Domains agreed with the consumer
Consumer-aligned domains are the opposite of source-aligned domains. They correspond to specific end user use cases that require data from other domains. Customer-agreed domains use and transform data according to your organization's use cases.
Consider providing shared data services to transform and consume data to meet these needs. You can offer domain-agnostic data infrastructure capabilities, such as data pipelines, storage infrastructure, streaming services, analytics, and more.
Redelivery domains
Data reuse is a different and more complex scenario. For example, if subconsumers are interested in combining data from different domains, you can create data products that aggregate data or aggregate high-level data needed by many domains. This avoids repetitive work.
Do not create reliable dependencies between data products and analytic use cases. Instead, strive for flexibility and free interdependence. The following model shows how to achieve flexibility. The domain takes responsibility for both data products and analytic use cases, and has developed separate processes for data product creation and data use. nine0015
Defining overlapping domain patterns
Domain modeling often becomes more complex when data or business logic is shared across domains. In large organizations, domains often use data from other domains. It can be useful to have generic domains that provide integration logic in a way that other subdomains can standardize and use. Keep the common model between subdomains small and always align with the universal language. nine0015
In large organizations, domains often use data from other domains. It can be useful to have generic domains that provide integration logic in a way that other subdomains can standardize and use. Keep the common model between subdomains small and always align with the universal language. nine0015
Different patterns can be used for overlapping data requirements other than domain-based architecture. Below is a brief overview of the templates that you can choose from:
- Single Method Template can be used if you prefer the associated cost of duplicating reuse. Reuse is sacrificed for higher flexibility and flexibility.
- Template customer supplier can be used if one domain is strong and willing to take ownership of the underlying data and consumer needs. Drawbacks include conflicting issues and forcing subordinate teams to negotiate deliverables and prioritize planning.
- Partnership template can be used if the integration logic is coordinated in an unplanned way in a newly created domain.
 All teams collaborate and consider each other's needs. Since no one is free to change the overall logic, a significant commitment is required from all participants. nine0004
All teams collaborate and consider each other's needs. Since no one is free to change the overall logic, a significant commitment is required from all participants. nine0004 - The matching template can be used to match all domains of all requirements. Use this pattern if 1) your integration is difficult, 2) other parties have no control, or 3) you are using vendor packages.
In all cases, your domains must comply with interoperability standards. A partnership domain that creates new data for other domains must provide its own data products, like any other domain, including ownership. nine0015
Domain Responsibilities
The Data Grid decentralizes ownership of data by distributing it across groups of domains. For many organizations, this means moving from a centralized management model to a federated model. Domain groups are assigned to tasks such as:
- Acquiring rights to data pipelines such as ingestion, cleansing, and transformation of data to serve as many data client needs as possible.
- Improving data quality, including compliance with service level agreements and quality measures set by data consumers
- Encapsulate metadata or use reserved column names to filter rows and columns precisely
- Compliance with metadata management standards, including:
- Registration of application schema and source system
- Metadata for enhanced discoverability
- Information about versioning
- Layout of data attributes and business terms
- Integrity of metadata information to improve integration across domains
- Compliance with data interaction standards, including protocols, data formats, and data types
- Provision of origin by linking origin systems and integration services to scanners or by manually providing origin
- Compliance with data sharing tasks, including IAM access checks and data contract creation
Level of detail for decompression
Now that you know how to recognize and facilitate data domains, you can learn how to design the correct level of detail for the domain and rules for unwrapping. When decomposing an architecture, two important dimensions are used. nine0015
When decomposing an architecture, two important dimensions are used. nine0015
The granularity for functional domains and the setting of bounded contexts is one dimension. Domains conform to a defined way of working, making data available across all domains through shared services, ownership, adherence to metadata standards, and more.
Specify fine-grained boundaries where possible for data distribution. Data-driven data mining is all about making the data available for heavy use. If you make your boundaries too loose, you force unwanted interdependencies between many applications and lose the ability to reuse data. Try to separate every time data crosses business opportunity boundaries. A domain allows tight coupling within the domain's internal architecture. However, when crossing business opportunity boundaries, domains must remain decoupled and distribute read-optimized data products to be shared with other domains. nine0015
The granularity for technical domains and infrastructure usage is another important dimension. Targeted data zones provide the flexibility to serve data applications that create data products. How to create such a target zone with common infrastructure and services? Functional domains are logically grouped and are good candidates for sharing platform infrastructure. The following are some of the factors to consider when creating these target areas. nine0015
Targeted data zones provide the flexibility to serve data applications that create data products. How to create such a target zone with common infrastructure and services? Functional domains are logically grouped and are good candidates for sharing platform infrastructure. The following are some of the factors to consider when creating these target areas. nine0015
- Cohesion and efficiency in data manipulation and sharing is a strong factor in aligning functional domains with the target data zone. This is due to data gravity, the tendency to constantly share large data products between domains.
- Regional boundaries may result in the implementation of additional target data zones.
- Ownership, security, or legal boundaries can force domain separation. For example, some data may not be visible to other domains. nine0004
- Flexibility and rate of change are important factors. Some domains may have a high rate of innovation, while other domains place a high value on stability.

- Functional boundaries can separate commands. An example of this would be source and consumer boundaries. Half of your domain teams may value some services over others.
- If you want to potentially sell or separate your capabilities, you should avoid integrating tightly with shared services from other domains. nine0004
- Team size, skills and maturity can be important factors. Highly skilled and mature teams often prefer to work with their own services and infrastructure, while less mature teams are less likely to appreciate the added cost of maintaining a platform.
Before provisioning multiple target data zones, examine the domain decomposition and determine which functional domains are candidates for sharing the underlying infrastructure. nine0015
Summary
Business Capability Modeling helps you better recognize and order domains in a data grid architecture. It provides a holistic view of how data and applications deliver value to your business, while helping you prioritize and focus on your data strategy and business needs. You can also use business opportunity modeling for more than just data. For example, if scalability is an issue, this model can be used to identify the most important core capabilities and develop a strategy for them. nine0015
You can also use business opportunity modeling for more than just data. For example, if scalability is an issue, this model can be used to identify the most important core capabilities and develop a strategy for them. nine0015
Concerns have been raised by some practitioners that creating a goal state architecture by comparing everything ahead is an intense exercise. Instead, they propose to define domains organically while connecting them to the new data grid architecture. Instead of defining a target state from top to bottom, you work down, learn, experiment, and move the current state to the target state. While this proposed approach may be faster, it carries significant risk. You can easily find yourself in the middle of a complex move or remodel operation when things start to break down. Working with both directions, top down and down, and then meeting in the middle over time is a more nuanced approach. nine0015
Next Steps
- What is a data product?
Application Domains - .
 NET Framework
NET Framework - Article
- Reading takes 9 minutes
Operating systems and runtime environments typically include some means of isolating applications from each other. For example, Windows uses processes to isolate applications. This isolation is necessary to ensure that code executed by one application cannot break other, unrelated applications. nine0015
Application domains form a sandbox for security, reliability, versioning, and assembly unloading. Application domains are typically created by the underlying runtimes, which are responsible for bootstrapping the common language runtime (CLR) before running an application.
Benefits of Application Isolation
Historically, process boundaries have been used to separate applications running on the same computer. Each application is loaded in a separate process that separates it from other applications running on the same computer. nine0015
Each application is loaded in a separate process that separates it from other applications running on the same computer. nine0015
Applications become isolated from each other because addresses in memory are tied to processes; it makes no sense to use in a process a pointer passed to it from another process. Also, direct calls between processes are not possible. Instead, you need to use proxies that provide a level of indirection.
Managed code must go through a validation process before it can run (unless the administrator gives permission to skip validation). The verification process determines whether the code may attempt to access invalid memory addresses or perform other actions that could lead to a violation of the correct operation of the process in which this code is running. Code that passes validation is called type-safe. The ability to check code for type safety allows the common language runtime (CLR) to provide the same high level of isolation between processes from each other as when using process boundaries, but at a significantly lower performance cost.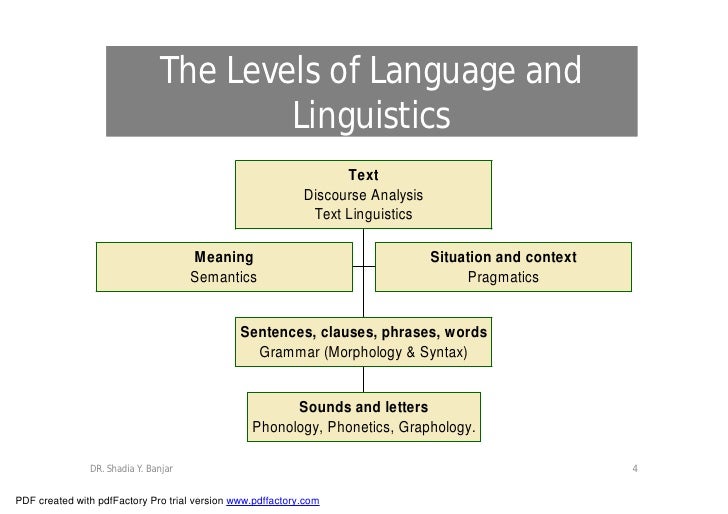 nine0015
nine0015
Application domains provide the common language runtime with more secure and flexible blocks that can be used to separate individual applications. You can run multiple application domains in a single process with the same level of isolation as individual processes provide, but without the overhead of inter-process calls or switching between processes. The ability to run multiple applications in a single process greatly increases server scalability.
Application isolation also plays an important role in security. For example, you can run multiple web application controls in the same browser process, so that the controls cannot access each other's data and resources. nine0015
Application isolation using application domains has the following benefits.
-
Failures in one of the applications will not affect other applications. Because type-safe code cannot cause memory faults, the use of application domains ensures that code running in one domain does not affect other applications in the process.
-
You can stop running individual applications without stopping the entire process. Using app domains allows you to offload code used by a single application. nine0015
Note
Unable to unload individual assemblies or types. You can only download the entire domain.
-
Code used by one application cannot directly access the code or resources of another application. The CLR implements this isolation by not allowing direct calls between objects in different application domains. Objects passed from domain to domain are copied or interact through a proxy. If an object is copied, the call to that object is local. That is, the caller and the callee are in the same application domain. If the object is accessed through a proxy, the object is called remotely. In this case, the caller and the callee are in different application domains. Cross-domain calls use the same remote calling infrastructure as calls between two different processes or two different computers.
 For a method call to be correctly JIT compiled, the metadata of the object being used must be available to both application domains. If the calling domain does not have access to metadata for the called object, compilation may fail with an exception of type FileNotFoundException. See Remote Objects for more information. The mechanism for determining the cross-domain access methods for an object depends on the object. See System.MarshalByRefObject for more information. nine0015
For a method call to be correctly JIT compiled, the metadata of the object being used must be available to both application domains. If the calling domain does not have access to metadata for the called object, compilation may fail with an exception of type FileNotFoundException. See Remote Objects for more information. The mechanism for determining the cross-domain access methods for an object depends on the object. See System.MarshalByRefObject for more information. nine0015 -
The behavior of the code is determined by the boundaries of the application in which it is running. In other words, the application domain provides configuration settings such as application versioning policies, the location of remote assemblies that are accessed, and where to look for local assemblies loaded into the domain.
-
Permissions granted to code can be controlled by the application domain in which the code is running. nine0015
Application domains and assemblies
This section describes the relationship between application domains and assemblies.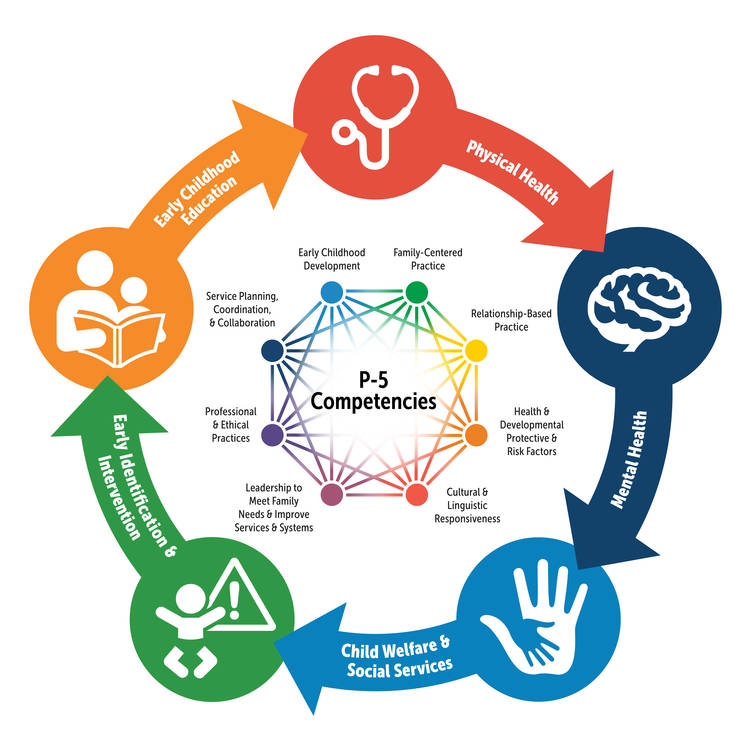 To execute the assembly code, it must be loaded into the application domain. Typically, multiple assemblies must be loaded into an application domain to run an application.
To execute the assembly code, it must be loaded into the application domain. Typically, multiple assemblies must be loaded into an application domain to run an application.
The loading method determines whether the JIT-compiled assembly code can be used across multiple application domains in a process and whether the assembly can be unloaded from the process.
-
When an assembly is loaded as domain-neutral, all application domains with the same security permission set can share JIT-compiled code, which reduces the amount of memory required by the application. However, an assembly cannot be unloaded from a process.
-
If an assembly is not loaded as domain-neutral, it must be JIT compiled in each application domain into which it is loaded. However, an assembly can be unloaded from a process by unloading all application domains into which it is loaded. nine0015
Whether assemblies should be loaded as domain-neutral is determined by the runtime host application when the runtime is loaded into a process. For managed applications, apply the LoaderOptimizationAttribute attribute to the process entry point method and provide a value from the associated LoaderOptimization enumeration. For unmanaged applications that host the CLR, set the appropriate flag when calling the CorBindToRuntimeEx function.
For managed applications, apply the LoaderOptimizationAttribute attribute to the process entry point method and provide a value from the associated LoaderOptimization enumeration. For unmanaged applications that host the CLR, set the appropriate flag when calling the CorBindToRuntimeEx function.
There are three options for loading domain-neutral assemblies. nine0015
-
LoaderOptimization.SingleDomain does not load assemblies as domain-neutral, except for Mscorlib, which always loads as domain-neutral. This option is called single-domain because it is typically used when the host application only runs one application per process.
-
LoaderOptimization.MultiDomain loads all assemblies as domain-neutral. Use this option when you have multiple application domains, each running the same code. nine0015
-
LoaderOptimization.MultiDomainHost loads strong-named assemblies as domain-neutral if they and all their dependencies are installed in the global assembly cache.
 Other assemblies are loaded and JIT-compiled separately for each application domain in which they are loaded, so they can be unloaded from the process. Use this option when you have multiple applications running in the same process, or if you have a set of assemblies that are shared across multiple application domains and assemblies that must be unloaded from the process. nine0015
Other assemblies are loaded and JIT-compiled separately for each application domain in which they are loaded, so they can be unloaded from the process. Use this option when you have multiple applications running in the same process, or if you have a set of assemblies that are shared across multiple application domains and assemblies that must be unloaded from the process. nine0015
JIT-compiled code cannot be shared between assemblies loaded into a loading context using the Assembly class's LoadFrom method or loaded from images using overloads of the Load method that specifies byte arrays.
Assemblies that have been compiled to native code using Ngen.exe (native imaging tool) can be shared across application domains if they are loaded as domain-neutral when first loaded into a process. nine0015
JIT-compiled code for an assembly containing an application entry point can only be shared if all of its dependencies can be shared.
A domain-neutral assembly can be JIT compiled more than once. For example, when two application domains have different security permission sets, they cannot share the same JIT-compiled code. However, each copy of a JIT-compiled assembly can be shared with other application domains that have the same set of permissions. nine0015
For example, when two application domains have different security permission sets, they cannot share the same JIT-compiled code. However, each copy of a JIT-compiled assembly can be shared with other application domains that have the same set of permissions. nine0015
When deciding whether to load assemblies as neutral, there is a trade-off between memory savings and performance.
-
Access to static data and methods for domain-neutral assemblies is slower due to the need to isolate assemblies. Each application domain that accesses an assembly must have its own copy of the static data to avoid object references in static fields that cross domain boundaries. As a result, the runtime contains additional rules for redirecting the caller to the appropriate copy of the static data or method. These additional rules slow down the call. nine0015
-
When you load an assembly as domain-neutral, you must find and load all of the assembly's dependencies, because a dependency that cannot be loaded as domain-neutral prevents the assembly from being loaded as domain-neutral.
Application domains and flows
An application domain forms a sandbox for security, versioning, reliability, and managed code unloading. A thread is an operating system construct used by the CLR to execute code. At runtime, all managed code is loaded into the application domain and executed on one or more managed threads. nine0015
There is no one-to-one correspondence between threads and application domains. Multiple threads can run in the same application domain at the same time, and a particular thread is not limited to a single application domain. Thus, threads can be used in different application domains. A new thread is not created for each application domain.
At any given time, each thread is running in an application domain. An application domain can have one or more threads running, or no threads running. The runtime keeps track of the threads and the application domains in which they run. At any point in time, you can find the domain in which the thread is running by calling the Thread. GetDomain method. nine0015
GetDomain method. nine0015
Application domains and culture
The culture represented by a CultureInfo object is associated with threads. To get the culture associated with the currently executing thread, use the CultureInfo.CurrentCulture property, and to get or set the culture associated with the currently executing thread, use the Thread.CurrentCulture property. If the culture associated with a thread is explicitly set using the Thread.CurrentCulture property, it will be associated with that thread outside of the application domain. Otherwise, the culture associated with the thread at any given time is determined by the value of the CultureInfo.DefaultThreadCurrentCulture property in the application domain where the thread is running:
-
If the value of this property is not
null, the culture it returns is thread-bound (and therefore returned by the Thread.CurrentCulture and CultureInfo.CurrentCulture properties). -
If the value of this property is
null, the current system culture settings are associated with the stream.
Programming with Application Domains
Application domains are typically created and managed programmatically by runtime host applications. However, sometimes applications themselves need to work with application domains. For example, an application can load a component into a domain so that it can unload the domain (and the component) without having to stop the entire application. nine0015
AppDomain is a programming interface for application domains. This class contains methods for creating and unloading domains, for instantiating types in domains, and for subscribing to various notifications such as unloading an application domain. The following table lists commonly used AppDomain methods.
| AppDomain method | Description |
|---|---|
| CreateDomain | Creates a new application domain. We recommend that you use an overload of this method that defines an AppDomainSetup object. This is the preferred way to set the properties of the new domain, such as the application's base or application root, the location of the domain's configuration file, and the search path used by the common language runtime to load assemblies into the domain. nine0384 nine0384 |
| ExecuteAssembly and ExecuteAssemblyByName | Builds in the application domain. This is an instance method, so it can be used to execute code in another referenced application domain. |
| CreateInstanceAndUnwrap | Creates an instance of the specified type in the application domain and returns a proxy. This method is used to avoid loading the assembly containing the generated type into the calling assembly. |
| Unload | Gracefully shuts down a domain. The application domain is not unloaded until all threads running in the domain are stopped or excluded from the domain. |
Note
The common language runtime does not support serialization of global methods, so you cannot use delegates to execute global methods in other application domains.
The unmanaged interfaces described in the Common Language Runtime Hosting Interfaces Specification also provide access to application domains. Runtime host applications can use interfaces from platform code to create and access application domains within a process. nine0015
Runtime host applications can use interfaces from platform code to create and access application domains within a process. nine0015
COMPLUS_LoaderOptimization environment variable
Environment variable that sets the default loader optimization policy for the executable application.
Syntax
COMPLUS_LoaderOptimization = 1
Standard application loads multiple assemblies into the application domain. After that, you can execute the code contained in them.
The loading method determines whether the JIT-compiled assembly code can be used by multiple application domains in the same process. nine0015
-
If the assembly is loaded as domain independent, then all application domains with the same security permission set can use the same JIT compiled code. In this case, the application uses less memory.
-
If an assembly is loaded as a domain dependent assembly, it must be JIT compiled in all relevant application domains, and the loader must use different internal resources in each case.

If the COMPLUS_LoaderOptimization environment flag is set to 1, then the runtime host application uses the SingleDomain loading method. It forces all assemblies to be loaded as domain dependent, except for the Mscorlib assembly, which is always loaded as independent. This option is called single-domain because it is typically used when the host application only runs one application per process.
Attention!
The COMPLUS_LoaderOptimization environment flag is for diagnostic and testing scenarios. When enabled, performance may slow down significantly and memory usage may increase. nine0015
Sample code
To have all assemblies for the IISADMIN service loaded as domain dependent, add the code COMPLUS_LoaderOptimization=1 to the multiline environment setting under HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\IISADMIN.
Key=HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\IISADMIN Name = Environment Type = REG_MULTI_SZ Value (to append) = COMPLUS_LoaderOptimization=1
See also
- System.

Learn more